CS 101
Passwords and Security
Announcements
- Paper due in 1 week. Come ask us questions!
- Last class is in a week. Week 10 Tuesday is a final review.
- Please fill out course evaluations.
- Common Homework Mistakes: the Friendship Paradox
Plan for Today
- What is encryption or security?
- Security in Society
- Hacks
- Protecting yourself
Security
- Protects data from prying eyes
- Encryption: puts the data in a secret code (ciphertext)
- Decryption converts the ciphertext to plaintext using a key
- This key is generated from your password
- Basic encryption: Caesar cipher
- Shift all the letters in the text by some number
- The number you shifted by is the key
- More complicated: One-time Pad
- Hacker's ultimate goal: get the plaintext
Hiding in plain sight: Steganography
- Can hide sensitive information inside other information (need to know what you're looking for)
- Encryption protects the message when overheard
- Steganography prevents the message from being found
Encrypted data
- Databases and user information
- Any "sensitive" data
- Internet traffic between clients and servers (https)
Public Key Encryption
- Motivation: How do you prove your identity on the internet?
- A website has a private key and gives out its public key
- Public key lets you check that the site is who they say they are
- Public key is issued by a certificate authority to limit impersonation
- Private keys are used to generate a shared key for the actual encryption
Types of Hacks
- Hacks to get passwords
- Phishing
- Dictionary Attack
- Hacks to steal information
- Viruses and Malware
- Man-in-the-Middle
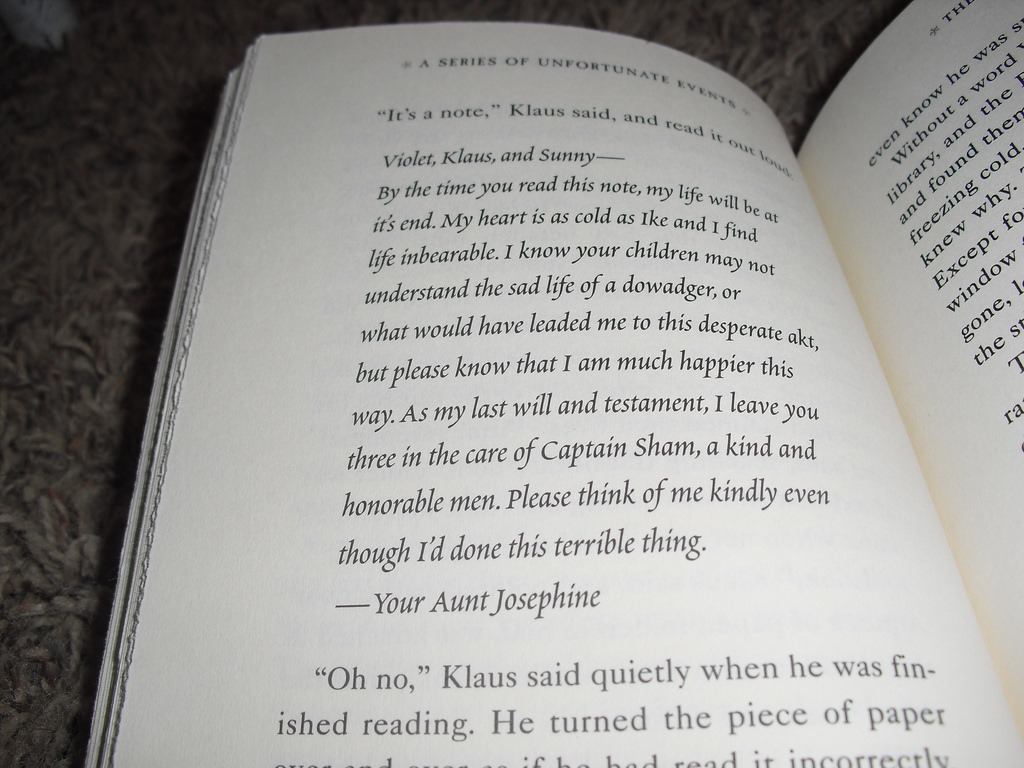
Social Attacks (Phishing)
- Attacker relies on goodwill/gullibility of people
- Redirect to a fake URL and get the user to type in a password (Google Docs)
- Impersonate someone else and ask for a password (Clinton Leaks)
- Counter: Always check the URL, and verify whom you give info to
- Other social attack: pretend to belong, and tailgate into a building
- Counter: it's better to be safe than to be nice
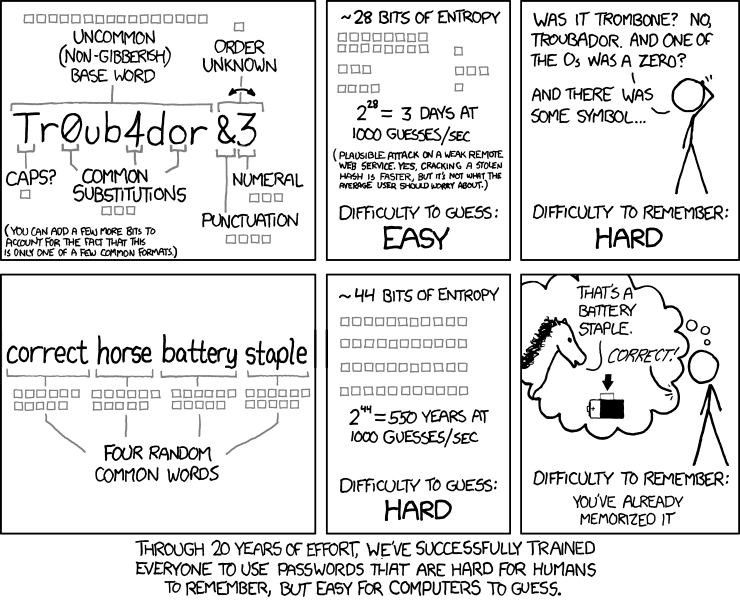
Dictionary Attack
- Try every known password
- Counter: programmers can build in a short delay so it takes longer to try passwords
- Counter: make your password unique AND long
Viruses and Malware
- Malicious program
- Can destroy your computer or steal your information
- Can cause your computer to join a Distributed Denial of Service (DDoS) attack, when a bunch of computers all make requests to the same server
- Counter: don't open email attachments unnecessarily
- Counter: firewalls on your computer and internet router
Man-in-the-Middle Attacks
- Eavesdrop on communication between computers
- Can edit the messages (impersonate one or both sides)
- Uses unencrypted Wi-Fi
- Counter: Transport Layer Security (TLS): security between the server and client (public key encryption)
Hashing
- What happens when there is a security breach?
- Sensitive information is "hashed" - turned into random-looking information
- Hash: mathematical function that takes in a plaintext, returns random-looking information
- Idea: instead of comparing the password entered to your password, we compare the hash of the entered password to your password
- Companies should only store hashed passwords
Passwords
- Unique between sites
- Long
- Use a password manager!
Multi-Factor Authentication
- Knowledge: something you know (password)
- Possession: something you have (device, such as a cellphone or yubikey)
- Bio-metric: something you are (fingerprint, retina scan)
Recap
- Encryption is used to protect data
- Hackers try to steal information by a variety of methods
- You can and should protect yourself