Security 1 - Passwords
Computer security is a big and kind of dramatic area which lends itself to movie plots and fear. There are real threats our there, but staying safe is not that hard.
Computer -- The Castle
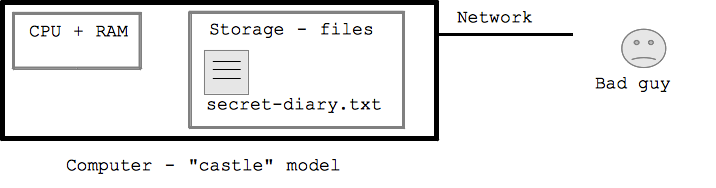
Computer Attacks
In the following sections we'll look at the three most common types of attack, lumping into broad categories: 1. Password attacks, 2. Phishing attacks, 3. Malware attacks.
Aside: Atypical Spear Phishing Case
Typical Bad Guy Attacks - Bulk
Although I'll talk about problems most of the time, don't get all scared. I use the internet all day long, I don't have any anti-virus software installed, and I have not had any problems (that I know of!). It probably helps that I don't run Windows which is a popular target and has had lots of problems.
Password Dictionary Attacks
A favorite CS101 question: list all the ways a bad guy can get your password? We'll go through them.
The bad guy could try to just guess your password, attempting to log in again and again, hoping to get lucky. They might know the username and just guess the password, or more likely they are guessing both. There are 86400 seconds in a day, and suppose your bank permits 1 login attempt per second. The bad guy could just go through the list of 100000 common passwords ("password", "password123", "janexyz", ...) trying to get lucky. This is good enough for the bad guys. Since they launch the attack in bulk, just getting a fraction of a percent is worthwhile.
Clearly, the bank or whatever should detect thousands of bad logins and slow down or freeze the account. This can cause problems for the legitimate user however, so it's a balance. One simple policy is that the Bank can process login attempts at a slowish rate, such one every second to prevent the bad guys from trying 100 billion different passwords.
Dictionary Attack Example
Here's a real "log file" from my codingbat.com server where it routinely records what happens each day. What you see here is the attacker is trying guess both the username and password on the account. It happens that the username for each attempt is printed in the log file but the password is not. No doubt they are trying common passwords, such as "secret" "password12" etc. It's funny to me that you can see that their list of usernames to try is sort of alphabetical order, and they are just running through it in the most obvious way. So what you need to understand is .. this sort of attack is clicking along, every second of every day aimed at basically all the servers on the internet. They just need to succeed with a few accounts here and there, even though they fail 99.99% of the time. This is why you should not have a password which is close to a dictionary word or someone's name, or is a password people often choose. The good news is .. with just 4 random letters added to your password .. suddenly this dictionary attack is not going to work -- there's not enough seconds in the day. Note that 49.212.7.205 is the IP address of the machine attacking codingbat.com. It appears to be in Japan -- it's probably some person's Windows machine that has been compromised and is now used as a "zombie" under the control of the bad guy to launch more attacks. The zombie is probably running attacks at many servers all at the same time, but here we just see the ones directed at codingbat, about one login attempt every 3 seconds.
... Mar 6 06:26:20 codingbat sshd[30924]: Failed password for invalid user alex from 49.212.7.205 port 36268 ssh2 Mar 6 06:26:22 codingbat sshd[30926]: Failed password for invalid user alex from 49.212.7.205 port 36605 ssh2 Mar 6 06:26:26 codingbat sshd[30928]: Failed password for invalid user alex from 49.212.7.205 port 36937 ssh2 Mar 6 06:26:29 codingbat sshd[30930]: Failed password for invalid user adam from 49.212.7.205 port 37212 ssh2 Mar 6 06:26:32 codingbat sshd[30932]: Failed password for invalid user fax from 49.212.7.205 port 37546 ssh2 Mar 6 06:26:34 codingbat sshd[30934]: Failed password for invalid user fax from 49.212.7.205 port 37864 ssh2 Mar 6 06:26:38 codingbat sshd[30936]: Failed password for invalid user demo from 49.212.7.205 port 38201 ssh2 Mar 6 06:26:41 codingbat sshd[30938]: Failed password for invalid user demo from 49.212.7.205 port 38561 ssh2 Mar 6 06:26:44 codingbat sshd[30940]: Failed password for invalid user amanda from 49.212.7.205 port 38911 ssh2 Mar 6 06:26:47 codingbat sshd[30942]: Failed password for invalid user angie from 49.212.7.205 port 39244 ssh2 Mar 6 06:26:51 codingbat sshd[30944]: Failed password for invalid user angie from 49.212.7.205 port 39552 ssh2 ...
Here's an example from 2017. This attacker is just guessing on the "root" account, which is a special powerful account on the server.
May 24 15:02:00 codingbat sshd[29281]: message repeated 4 times: [ Failed password for root from 202.109.143.15 port 1989 ssh2] May 24 15:02:01 codingbat sshd[29281]: Connection reset by 202.109.143.15 port 1989 [preauth] May 24 15:02:01 codingbat sshd[29281]: PAM 4 more authentication failures; logname= uid=0 euid=0 tty=ssh ruser= rhost=202.109.143.15 user=root May 24 15:02:01 codingbat sshd[29281]: PAM service(sshd) ignoring max retries; 5 > 3 May 24 15:02:11 codingbat sshd[29300]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=202.109.143.15 user=root May 24 15:02:14 codingbat sshd[29300]: Failed password for root from 202.109.143.15 port 3215 ssh2 May 24 15:02:21 codingbat sshd[29300]: message repeated 4 times: [ Failed password for root from 202.109.143.15 port 3215 ssh2] May 24 15:02:21 codingbat sshd[29300]: Connection reset by 202.109.143.15 port 3215 [preauth] May 24 15:02:21 codingbat sshd[29300]: PAM 4 more authentication failures; logname= uid=0 euid=0 tty=ssh ruser= rhost=202.109.143.15 user=root May 24 15:02:21 codingbat sshd[29300]: PAM service(sshd) ignoring max retries; 5 > 3 May 24 15:02:24 codingbat sshd[29319]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=202.109.143.15 user=root May 24 15:02:26 codingbat sshd[29319]: Failed password for root from 202.109.143.15 port 1800 ssh2 May 24 15:02:35 codingbat sshd[29319]: message repeated 4 times: [ Failed password for root from 202.109.143.15 port 1800 ssh2] May 24 15:02:35 codingbat sshd[29319]: Connection reset by 202.109.143.15 port 1800 [preauth] May 24 15:02:35 codingbat sshd[29319]: PAM 4 more authentication failures; logname= uid=0 euid=0 tty=ssh ruser= rhost=202.109.143.15 user=root May 24 15:02:35 codingbat sshd[29319]: PAM service(sshd) ignoring max retries; 5 > 3 May 24 15:02:43 codingbat sshd[29352]: pam_unix(sshd:auth): authentication failure; logname= uid=0 euid=0 tty=ssh ruser= rhost=202.109.143.15 user=root May 24 15:02:45 codingbat sshd[29352]: Failed password for root from 202.109.143.15 port 4832 ssh2
Aside: Geo IP
Where are these dictionary attacks coming from? It's a necessary part of TCP/IP that the other end needs to reveal its IP address to get IP packets back. Here we see it's: 202.109.143.15
Find a "geo ip" service - approximately where an IP address is on earth. Look up the address attacking us.
Weak Passwords
Weak Passwords - The Bad Guy Perspective
Strong Passwords
Outside Password Guessing vs. Cracking Stolen Passwords
What To Do
For an important site like a bank, you should use a password different from your other passwords. It should not be the case that by stealing your facebook or twitter password, they now have access to your bank. I write the passwords down on a piece of paper at my house in case I forget. The bad guy in Russia or whatever does not have some team of ninjas that's going to break into my house and get passwords off my slip of paper. The attacks are bulk, mindless affairs that work on the low-hanging fruit. One technique for writing down passwords is to pick a little suffix you memorize, like "x936" or whatever, and that always goes on the end of your passwords. Record the passwords down, but never the suffix. That way, even with the piece of paper, a bad guy still does not have the passwords. Or maybe its better to just write the passwords out clearly, so your family can access your email etc. if you are in the hospital.
Email is tricky -- once they have your email password, then they may be able to do a password reset and get into your account. In that sense, your email password is the most important.