Security 7 - Tracking
Computer security is a big and kind of dramatic area which lends itself to movie plots and fear. There are real threats our there, but staying safe is not that hard.
IP Addresses - Tracking
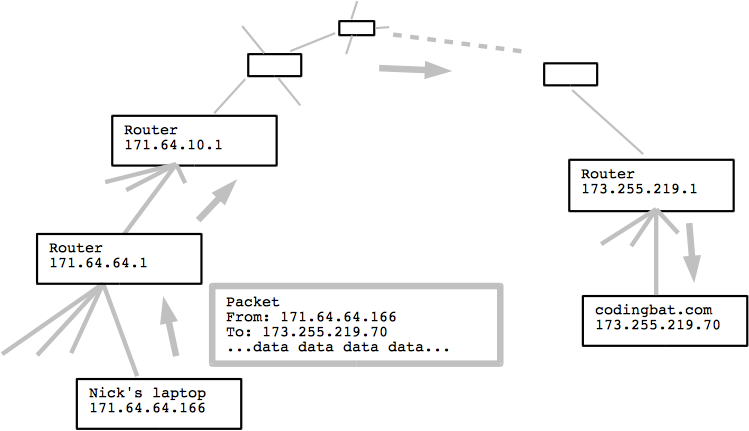
- Previously: every computer on the internet uses an IP address
e.g. 171.64.64.110 - Each packet has from: and to: IP addresses
- That's how they get back and forth!
- IP address is assigned by the internet-provider
- IP address generally can be traced to a city or perhaps building
(The service provider has the most info, not necessarily public) - Geo ip http://www.geoipview.com/
Scenario 1 - Server Log IP
- Web browser contacts web server
- Both have IP addresses!
- A server logs the browser IP of every request it gets in "log files"
- e.g. criminals are using some server to communicate
-The FBI gets the logs, tries to figure out who each IP is
-IP address is not a person
-FBI will need additional info to say who is behind an IP
Scenario 2 - VPN
- VPN - Virtual Private Network
- A tunnel for packets
- Hides the true source of a packet
- The packet appears to be from the VPN endpoint
- e.g. I am in Hawaii but want Stanford to think I'm in Palo Alto
1. Establish VPN tunnel with end-1 in Hawaii and end-2 in Palo Alto
2. From Hawaii packet goes through VPN tunnel and on to the server
3. As seen by the server, the packet is from: end-2, hiding my location - A VPN can also feature encryption
- However HTTPS does that more easily
- Many people in China use VPNs to get content from the internet at large
- Famous ironic example: creator of China firewall has web access blocked in talk
has to use VPN
Blocking the internet to shape people's thoughts is dumb!
http://time.com/4283248/china-great-firewall-fang-binxing-censorship/
Scenario 3 - China
- China's government seeks to control what info is on the internet
- At the router level, government controls routers between china and the world
- A the simple step, block packets going to wikipedia, youtube, nytimes
- More intrusive: look inside packets, track down prohibited speech
-https can protect the packets
-but not if China requires citizens to use government controlled service
-Orwellian!