Assignment 8: Cell Phones, Iridium, and Your Final Project
Overview
This week we will spend a little time of cell phones, and how they work. Then we will spend some time looking at Iridium, the satellite phone company. This is a nice example of many features of 3G cell phone systems. Finally, we'll talk about topics for your final project.
Cell Phones
Mobile phones have be around since before WWII. These systems used a relatively low frequency, and only a few channels. This meant that only a few simultaneous connections could take place at once. Originally these were bulky and heavy, but by the early 1970's handheld models appeared. Calls were very expensive due to the limited network capacity.
Cellular Phone Systems
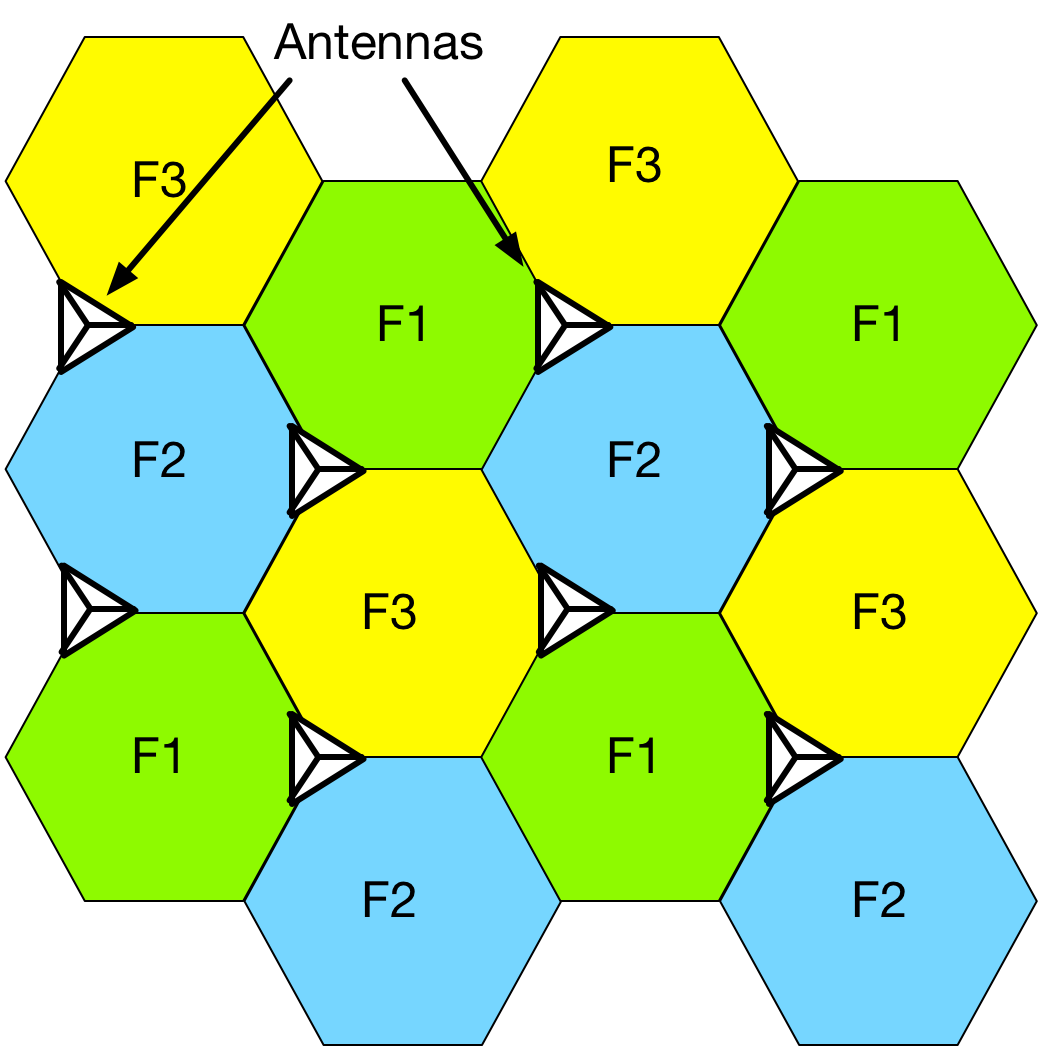
The key to breaking the limitation of only a few frequencies was the concept of cellular phones. The idea is to divide the coverage area into small regions, or cells. Each cell uses a different frequency than its neighbors, so they don't interfere. However, cells that are two cells away reuse the original frequency again. Cells of three frequencies can then tile a very larger area. The idea is illustrated below

No adjacent cells share a frequency, but only three frequencies are needed to cover everything. In practice, more frequencies will be used, because the cells are actually layed out to cover where people are (like along highways), and that doesn't tile as perfectly.
Most cell towers use directional antennas, because the FCC allows the output power to be 500 Watts for a directional antenna, compared to 100 Watts for an omnidirectional antenna. A typical directional antenna has three faces, which can be placed at the corners of the cell to produce relatively uniform coverage.

The area of the cells is determined by the frequency if the power is fixed. Early cell phones used frequencies in the 450 MHz range, which goes a long way. Cells were large, and not many calls could be made in a geographic area. As frequencies get higher the signal goes less far, the cells get smaller, and the capacity of the network increases. One example from Wikipedia is shown in the table below
| Freq (MHz) | Cell radius (km) | Cell area (km2) | Cell Count |
| 450 | 48.9 | 7521 | 1 |
| 950 | 26.9 | 2269 | 3.3 |
| 1800 | 14.0 | 618 | 12.2 |
| 2100 | 12.0 | 449 | 16.2 |
We get 16 times more capacity at 2100 MHz as at 450 MHz. This is a tremendous benefit in urban areas. The rapidly coming 5G systems will be at 28 GHz and 34 GHz. These will be even more local, much higher signal bandwidth, exploit multiple transmit and receive paths (MIMO), and have tremendously higher capacity as a result.
Cell Phone Radio
Cell phones are again a digital packet radio system. The packet data is encoded either using spread spectrum techniques (CDMA) or using multiple frequency shifted carriers (OFDMA, a multi-user variant of OFDM), just like the techniques we saw in WiFi last week.
In Wifi, everyone on a subnet talks on a single frequency. For cell phones, the uplink and downlink are separated. They may be on different frequencies (common in the US) or they may share a frequency by multiplexing (common in China). Multiplexing has the advantage that usually the bulk of the traffic at any instant will be one way, or the other. The multiplexing can dynamically favor the higher data rate direction, and make better use of the spectrum.
Starting with 3G systems (2000's) the control and data parts of the cell phone signal were encoded as IP, just like WiFi. The voice signal was still switched separately due to concerns about latency in packet switched networks. With 4G (the 2010's) everything went to IP including voice. This followed the same transformation on wired lines. Effectively the 4G phone system is WiFi with a special radio transport layer. Remarkably, that means you can use WireShark to watch the traffic on a cell phone network!
3G Networks
3G networks were interesting to capture with your SDR. Although not in use in the US right now, it is still used elsewhere in the world. There is one major exception, that we'll talk about shortly. 3G networks use a control channel that is responsible for housekeeping like setting up and taking down calls, and assigning frequencies. This is transmitted in the clear, so that if you can capture and decode the 3G signal, you can feed the result into wireshark, and look at who is connecting to who, and what the traffic looks like. Unfortunately, I don't know how to do this with a 4G net. Others have figured this out, which is a potential project.
One place where 3G still is used is Iridium. This is the satellite phone system originally launched in 1998. This operates in the 1.61885 to 1.6265 GHz band, which is within the range that your rtl-sdr can acquire. You will need an antenna tuned to that frequency (a patch antenna is good), and a low noise amplifier (LNA) right next to the antenna in order to avoid losing too much signal in the cable.
This youtube video describes how the Iridium system works, and how the signals can be acquired and decoded. This is done a German group. Some of what they show is illegal here (decoding pager messages, for example).
Note that this was done with the original Iridium satellites that are now being replaced with IridiumNext. I had expected that many of these issues would have been fixed, but that doesn't seem to be the case. Certainly anyone using the legacy modes is still vulnerable.
Final Project
The final project will be very much like the weekly assignment. You can work in groups of two to three if you'd like. Ideally there would be about five or six groups. Aim for about 20 slides, and about 20 minutes, with another 5 minutes for questions. You will present these during the last week of class. If you do work in groups, include a slide about what each person contributed (don't show this in the presentation).
For this week, look over the topics, and choose one. Make 2 slides about what the topic is, and why it is interesting. Upload your slides here
We'll go over them in class on Tuesday. You will have Thursday to work with your group, look up resources, and ask questions about your projects.
Possible Topics
All computers, keyboards, and monitors put out RF signals, as well as others. These can be captured, and the activity of the device decoded. This can include keylogging, and reconstructing the appearance of a display. This can all be done at some distance. The U.S. National Security Agency refers to this as Tempest, and has spent years both exploiting this, and shielding devices from this.
There are several options here.You can look up the history of Tempest, and what sort of vulnerabilities have been found and exploited.
There are lots of recent attempts using rtl-sdr's for Tempest. One of the first is described here
TempestSDR
and here is a more recent posting. These articles have an overview, some videos, a pointer to the software, and a pointer to Martin Marinov's MPhil dissertation on this topic. The newer article has a pointer to the github repository that contains code as well as sample data, and links to lots of additional articles. This works with your rtl-sdr, although a higher end sdr will give you better pictures.
The Iridum video above was from a couple of years ago. This IEEE Spectrum Article from a couple weeks ago describes where things are now. What has been fixed? What remains the problematic? How much progress have the CCC people made since the video was made?
The software we used for the RTL-SDR's comes from a project called OSMOCOM, for Open Source Mobile Communications. They do lots of interesting things. One place to start is the Osmocom Wikipedia Page, which has a link to their web page and github. If you look at the “projects” tab you will see some of the things they are working on. You'll find a link to the rtl-sdr software we use here with lots of additional information about how it works and what else you can do with it. Desribe some of the projects that they are working on, and why they are interesting.
Edward Snowden sure didn't make a lot of friends at the NSA! He exposed a number of very important intelligence gathering programs. Although many of these were rumored to exist, he provided confirmations, and a lot of detail about how they work and what they do.
Options for this project are:Overall, why was the NSA so upset? Why was the tech industry so upset? Why were other countries so upset? What has changed since? An example of one area is server farms, how they are encrypted, and where they are located.
Choose one of the programs he exposed. What did this program do? How did it work technically? What is the significance of its compromise? How has the tech industry responded?
What are the regulations for the U.S. government for eavesdropping on foreign nationals, and U.S. citizens? What approvals are needed, and who provides oversight? What role do the telecom companies play? This was just recently the subject of legislation.
There are limits to what data federal agencies can collect on you. However, the can buy your data from data brokers.
Where does this data come from? Why would anyone consent to this?
Who are these data brokers?
This turned up in the aftermath of the events of Jan 6. What was the story? Are there any other recent examples of this? This article describes the potential capabilities and problems with this technology.
Using Location Data for Tracking Jan 6 Attackers
One way to intercept cell phone calls is with a Stingray system manufactured by the Harris Corporation. These simulate a cell phone tower, and trick the cell phone into connecting with it. The Stringray box then forwards the call to the real cell phone system, so the call goes through like usual. The Stingray box can then decode the entire call.
How do these systems work? How does it defeat the cell phone encryption? The wikipedia page is a good place to start
Stingray Systems
If you wanted to make one yourself, how hard would it be?These devices show up in the press frequently, and are often a very contentious issue. One issue is that even the use of these devices is often denied. A recent Wired article describes a group in Seattle that developed a method for tracking these systems down
Stingray Tracking
Starting with this article, look at what the issues with these systems are. One example is this Mercury News article about the response when Santa Clara County (where we are!) bought one:
Stingray Systems in Santa Clara
One point I like is that even the people who are buying the system don't know exactly what they can do!
Pagers used to be quite the thing at the time when TV show “The Wire” was set. They continue to be widely used. Because many of the frequencies are fairly low (VHF to low UHF) the pager signals penetrate building much better than cell phones. This is important for people who care about reliability. They are also built into all sorts of monitoring systems for buildings, machinery, or computer systems.
Describe how the pager systems are structured. How is the information transmitted to the pager? How can you decode the signals? The most common pager standard is POCSAG. See if you can find any public domain software to decode the signals. Don't intall this, though, it is illegal. There are lots of YouTube videos that show you what you will see.
There was a recent story about someone in Kansas who did download pager traffic, saw lots of stuff from the local hospitals, and alerted the local newspaper. He was threatened with prosecution by one of the hospitals! That really fixed the problem. The story is here.This class has shown you some of the ways you are exposed during your normal day-to-day life. How can you minimize this while still leading a fairly normal life? What would be your major concerns? What would you do differently? How about if you wanted to really minimize your exposure? This Wired article is a place to start. This YouTube video talks about some of the issues with modern cars.
Find your own topic on the use and abuse of RF signals! There are lots of other examples out there.